Tracelay OWASP Top 10 For Android - Java
Learn common security threats & vulnerabilities encountered and detailed best practices for Android development with Java.
-
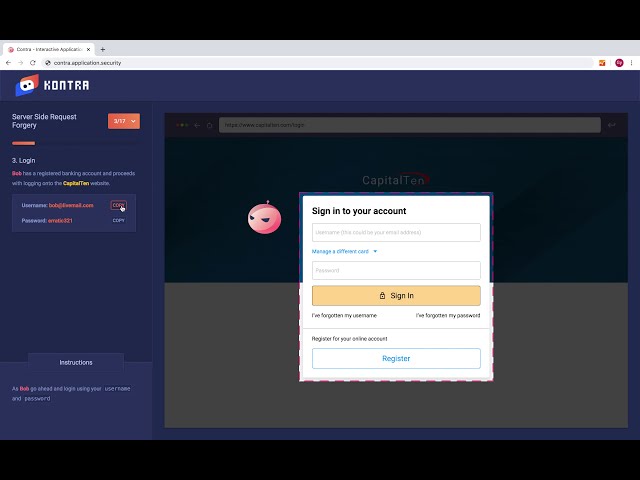
Improper Credential Usage
NEW
-
Inadequate Supply Chain Security
NEW
-
Insecure Authentication-Authorization
NEW
-
Insufficient Input-Output Validation
NEW
-
Insecure Communication
NEW
-
Inadequate Privacy Controls
NEW
-
Insufficient Binary Protections
NEW
-
Security Misconfiguration
NEW
-
Insecure Data Storage
NEW
-
Insufficient Cryptography
NEW