Tracelay OWASP Top 10 for Kubernetes
Learn common security threats & vulnerabilities encountered and detailed best practices for Kubernetes.
-
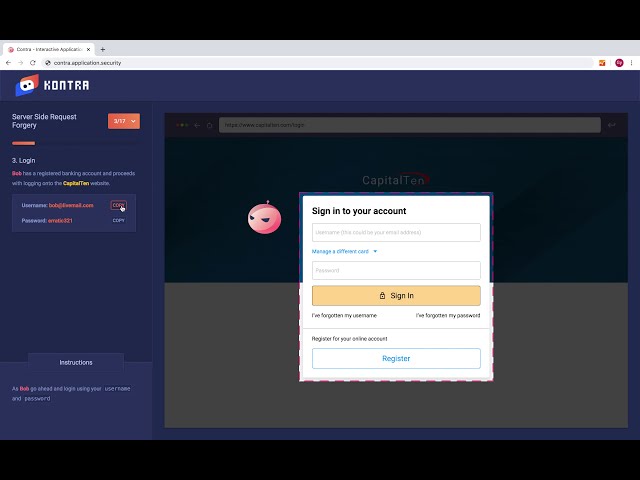
Broken Authentication Mechanisms
NEW
-
Inadequate Logging and Monitoring
NEW
-
Insecure Workload Configurations
NEW
-
Lack of Centralized Policy Enforcement
NEW
-
Misconfigured Cluster Components
NEW
-
Missing Network Segmentation Controls
NEW
-
Overly Permissive RBAC Configurations
NEW
-
Secrets Management Failure
NEW
-
Supply Chain Vulnerabilities
NEW
-
Vulnerable Kubernetes Components - Security Audit
NEW